Algorithms and Theory at Khoury College of Computer Sciences
Advancing knowledge about the foundations of computing
The Algorithms and Theory research area at Khoury College focuses on fundamental questions in computer science, developing knowledge that supports progress in any specialty: for instance, determining what it means for something to be computable, what kind of computations can be made, investigating whether in principle sets of procedures — algorithms — can be created for a type of problem, and analyzing those algorithms’ characteristics.
In this way, algorithms and theory research supports computer science across a range of other areas such as fueling cryptography, AI, and data science, areas where practitioners building tools need to know that the foundational theory their work depends on is sound, what the limits are, and what’s feasible.

Pushing the boundaries of what’s possible
Insights from Khoury College algorithms and theory research have an impact on many aspects of computing. In particular, theory research has helped discover how cryptography can help keep information you look up from a resource private, with the potential that someday you could use a search engine but it wouldn’t see what you’re doing — a potential revolution in privacy.
Study of algorithms can help ground core work in software development. By looking at the general and abstract characteristics of a computational problem, you can assess its complexity and what the limits may be to creating algorithms to tackle it. In this way, Khoury College is helping build the foundation for better approaches to building programs and tools, pushing the boundaries of what is feasible technically through better understanding of theoretical limits.
Sample research areas
- Algorithms for massive data
- Approximation algorithms
- Computational complexity
- Cryptography
- Distributed computing
- Cybersecurity and privacy
- Learning theory
- Network algorithms
- Quantum computation
Khoury researchers: At the forefront
Faculty awards and achievements
Best paper
- STOC 2025: Soheil Behnezhad
- SODA 2024: Soheil Behnezhad
- STOC 2023: Daniel Wichs, Wei-Kai Lin, Ethan Mook
- CCC 2008: Emanuele Viola
Best student paper
- ITCS 2023: Lunjia Hu
- ALT 2022: Lunjia Hu
Honors and awards
- Sloan Fellow 2018: Daniel Wichs

Featured project highlights
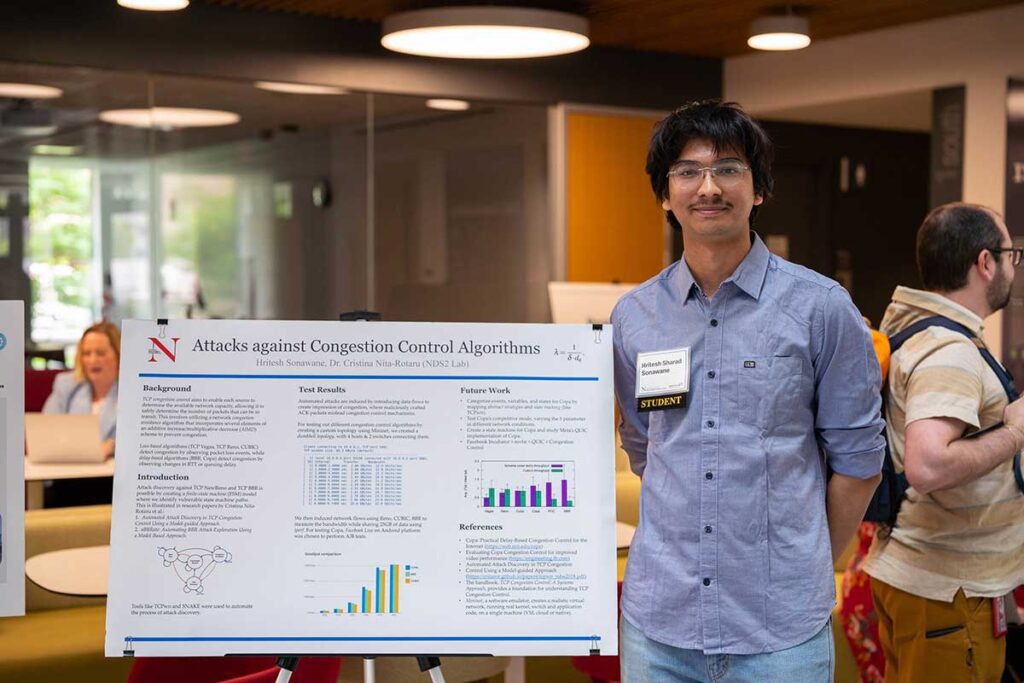
Foundations of Processing Massive Data
Modern algorithms must efficiently process unprecedented volumes of data. But this shift alters the fundamental principles of computation and algorithm design, requiring entirely new paradigms for handling massive data. While traditional algorithms assume all of the input is stored in the memory of a single computer that processes it, this assumption is far from what happens in practice where the input is distributed across a large number of machines. Khoury faculty study the foundations of this paradigm shift from various aspects.
Foundations of Trustworthy Machine Learning and Data Science
How can we trust data driven systems in high-stakes applications? Khoury faculty are addressing this challenge by developing the theoretical and conceptual foundations of trust in AI, machine learning, and data science. This work addresses problems like privacy of the data that drives these systems, reliably quantifying their uncertainty and making sound decisions from their outputs, and hardening these systems to be robust even to malicious attackers.
Encrypting Data and Still Working With It
Can we privately search the internet without revealing our query to the search engine? Khoury faculty are working on novel methods to encrypt data while enabling third parties to perform private computations over it. These technologies have the potential to allow for innovative applications from secure internet search to secure data analytics, vastly increasing our privacy on the internet.
Understanding the Limits of Efficient Computation
Can we understand the limits of efficient computation? This question is one of the grand challenges in computer science and mathematics, which profoundly shapes the computer systems we use daily. Computer systems must navigate around computationally intractable problems, while modern cryptography depends on problems that we believe are computationally hard. Khoury faculty approach this challenge by forging new connections between computational problems and establishing unconditional impossibility results within restricted yet far-reaching models.
Related labs and groups
Faculty members
-
Soheil Behnezhad
Assistant Professor
Soheil Behnezhad is an associate professor at Khoury College. He is broadly interested in theoretical computer science, with much of his work focused on graph algorithms and the theoretical foundations of big data algorithms.
-
Mahsa Derakhshan
Assistant Professor
Mahsa Derakhshan is an assistant professor at Khoury College. She is broadly interested in the design and analysis of algorithms, specifically algorithms under uncertainty.
-
Wolfgang Gatterbauer
Associate Professor
Wolfgang Gatterbauer is an associate professor at Khoury College. He works on the theory of scalable data management, with the goal of expanding data management systems and enabling them to support novel functionalities.
-
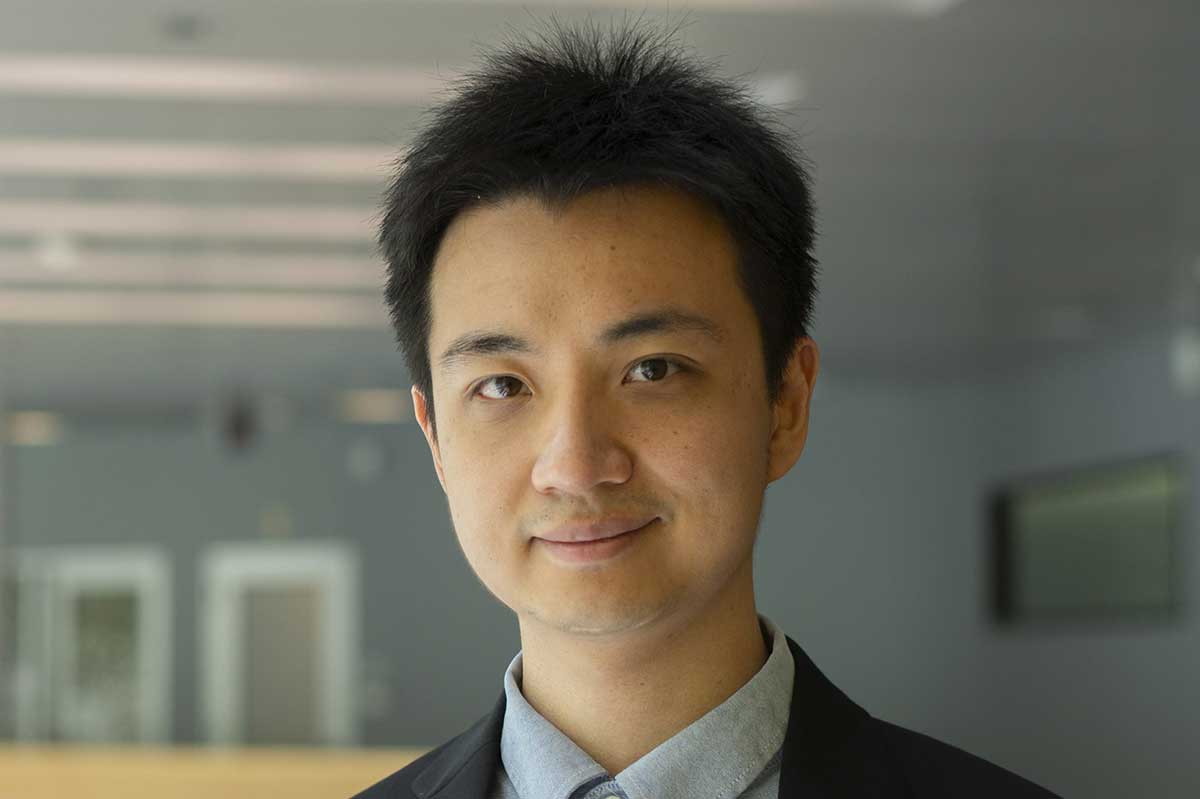
Zhengzhong Jin
Assistant Professor
Zhengzhong Jin is an assistant professor at Khoury College. He is interested in cryptography, teaching courses on the subject, and researching a proof system to delegate heavy computation to an untrusted server while ensuring the computation is correct.
-
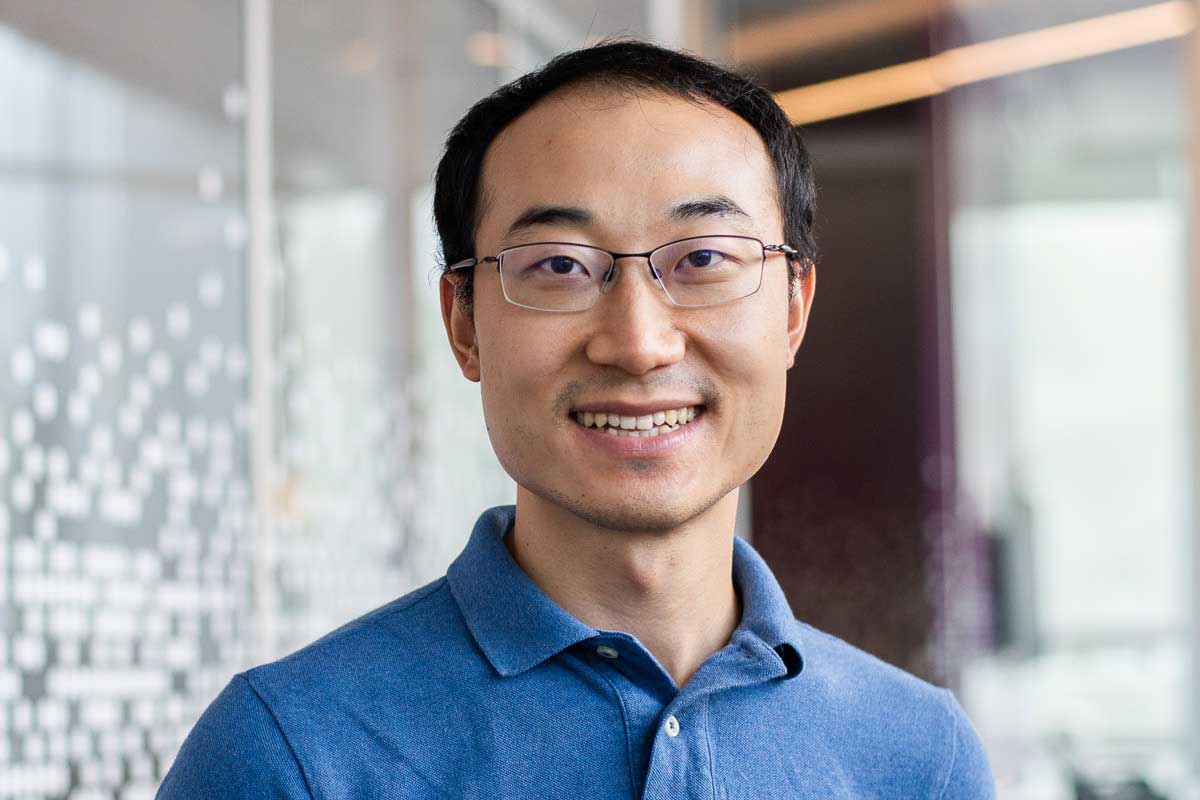
Huy Lê Nguyen
Associate Professor
Huy Lê Nguyen is an associate professor at Khoury College. He researches the design and analysis of algorithms, with an emphasis on algorithmic techniques for machine learning and massive data sets.
-
Rajmohan Rajaraman
Professor, Associate Dean of Faculty Affairs
Rajmohan Rajamaran is a professor and the associate dean of faculty affairs at Khoury College. He has made important contributions in the areas of distributed hash tables and fundamental combinatorial optimization problems, with the former being incorporated in peer-to-peer systems.
-
Abhi Shelat
Professor
Abhi Shelat is a professor at Khoury College specializing in cryptography and applied security. A recipient of awards from the NSF, Microsoft, Amazon, Google, and the ACM, he uses secure computation protocols to enable mutually distrusting parties, each with private inputs, to jointly compute functions while ensuring maximal privacy and correctness.
-
Ravi Sundaram
Professor
Ravi Sundaram is a professor at Khoury College and the former director of engineering at Akamai Technologies, where he helped build the world’s leading content delivery network. In his network and algorithms research, he devises efficient schemes to improve the performance of network-based applications.
-
Jonathan Ullman
Associate Professor
Jonathan Ullman is an associate professor at Khoury College whose research centers on the foundations of privacy for machine learning and statistics. Ullman has been recognized with an NSF CAREER award and the Ruth and Joel Spira Outstanding Teacher Award.
-
Emanuele Viola
Professor
Emanuele “Manu” Viola is a professor at Khoury College. Viola’s theoretical computer science research has included a wide variety of areas, including pseudo-randomness, cryptography, data structures, communication complexity, and circuit lower bounds. He has made fundamental contributions to the field, including solving long-standing open problems.
-
Daniel Wichs
Professor
Daniel Wichs is a professor at Khoury College. An expert in modern cryptography, Wichs researches all aspects of the field, including its theoretical foundations and its applications to information security. Wichs’ work was recognized in 2018 with the prestigious Sloan Research Fellowship, which honors early-career scholars whose achievements mark them among the top scientific minds.
-
Hongyang Zhang
Assistant Professor
Hongyang Zhang is an assistant professor at Khoury College. He researches at the nexus of machine learning, algorithms, and statistics, and has helped to develop techniques for neural networks, data augmentation, and transfer learning.