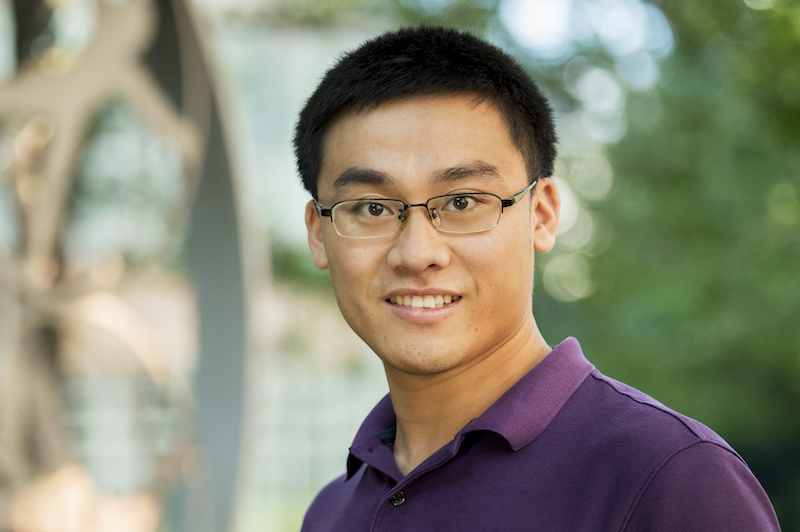
Zhichuang Sun
PhD Student
Research Interests
- Security and Privacy
- Systems and Networking
- Programming Languages
Education
- MS, Peking University - China
- BS, Huazhong University of Science and Technology - China
About Me
- Hometown: China
- Field of Study: System Security
- PhD Advisor: Long Lu
Biography
Zhichuang Sun is a PhD student in the System Security program at Northeastern University’s Khoury College of Computer Sciences, advised by professor Long Lu. Sun, a native of China, joins Northeastern after earning his Bachelor’s of science from Huazhong University of Science and Technology and his Master’s of science from Peking University. His research interests include programming languages, security and privacy and systems and networks. He is a member of the RiS3 lab.
Sun is interested in security because it's becoming more and more important, challenging and interesting. He is currently working on the combination of systems and security, on the remote attestation of IoT devices -- thinking about how to efficiently verify the security status of IoT devices that are currently deployed everywhere around the world.
What are the specifics of your graduate education (thus far)?
System Security, especially IoT device security.
What are your research interests?
Generally I'm interested in security because it's becoming more and more important, challenging and interesting. I used to be interested in systems, and I love building system software like Operating Systems and Compilers because they are more important and challenging than applications and they are the foundation that applications rely on. I used to join in the development of open-source operating systems and emulators. Now I'm working on the combination of systems and security, and my systems background helps a lot in system security research. To be more specific, I work on remote attestation of IoT devices, thinking about how to efficiently verify the security status of IoT devices that are deployed everywhere nowadays.
What’s one problem you’d like to solve with your research/work?
Offering strong security guarantees for IoT devices in an efficient way.
What aspect of what you do is most interesting?
We will use a lot of program analysis techniques to assistant programmers in augmenting the program, which makes applying our system easier. We also try to take advantage of hardware features of IoT devices, so that the trust of the system will be rooted in hardware.
What are your research or career goals, going forward?
I have two dreams, the first one is to be a professor, the second is to start a company of my own. To be a good professor requires me to be a smart and hardworking PhD.
Recent Publications
-
Mind your weight(s): A large-scale study on insufficient machine learning model protection in mobile apps
Citation: Sun, Zhichuang, et al. "Mind your weight(s): A large-scale study on insufficient machine learning model protection in mobile apps." 30th USENIX Security Symposium (USENIX Security 21). 2021. -
OAT: Attesting Operation Integrity of Embedded Devices
Citation: Zhichuang Sun, Bo Feng, Long Lu, and Somesh Jha. "OAT: Attesting operation integrity of embedded devices." In 2020 IEEE Symposium on Security and Privacy (SP), pp. 1433-1449. IEEE, 2020. DOI: 10.48550/arXiv.1802.03462 -
Dominance as a New Trusted Computing Primitive for the Internet of Things
Citation: Meng Xu, Manuel Huber, Zhichuang Sun, Paul England, Marcus Peinado, Sangho Lee, Andrey Marochko, Dennis Mattoon, Rob Spiger, Stefan Thom (S&P/Oakland'19)