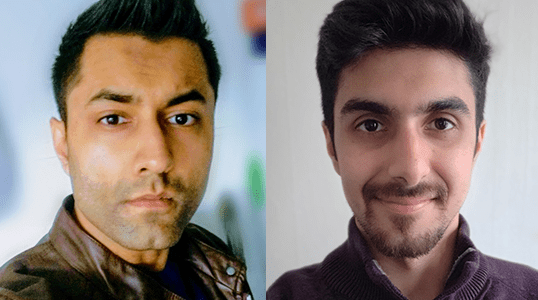
Jose Sierra
Teaching Professor, Associate Director - Cybersecurity and Information Assurance Graduate Program

Research interests
- Attribute based access control
- IoT communications protection
- Technology innovations in cyber threats and cyber defenses
Education
- PhD in Computer Science, Carlos III University of Madrid — Spain
- MS in Computer Science, Málaga University — Spain
- MS in Business Administration, Rey Juan Carlos University — Spain
- MIT Professional Education Certificate in Applied Cybersecurity, Massachusetts Institute of Technology
Biography
Jose Sierra is a teaching professor and the associate director of the Information Assurance and Cybersecurity program at the Khoury College of Computer Sciences at Northeastern University. He earned his master’s in business administration from Rey Juan Carlos University and his master’s in computer science from Málaga University. Sierra obtained his doctorate in computer science from Carlos III University of Madrid.
His research interests have been centered on the design, implementation and management of security services for interconnected systems. Initially, they were based on the foundations of some cryptographic algorithms and later focused on their use for the implementation of security protocols. In recent years, Sierra’s research has evolved to cybersecurity management and how organizations can take strategic decisions, which will help them to counteract cyberthreats. Other areas with remarkable results were Vehicular Ad-Hoc Networks (VANETs) protection, P2PSIP security architecture and low-performance computing devices used in Wireless Sensor Networks.
Sierra’s research group, the EVALUES IT Security Laboratory, was triggered by the evaluation of his research in the validation and evaluation of security protocols. His work evolved from formal validation logics for security protocols to assessment methodologies for commercial implementations of IPSEC architecture.
Projects in the aerospace defense sector:
- Innovative AAA System for Interoperable Distributed Architectures.
- Design and implementation of a Security Compliance Accreditation plan for Defense Simulation Laboratory.
- Design and implementation of a Secure Communication library for ground systems data synchronization.
- Development of Smartcard based Identification and Authentication System for multiplatform ground systems.
Projects in the realm of national and European-funded research:
- Advances for the city of the future: sustainable, smart and efficient. WP1 Security Architecture (Ciudad 2020)
- Smart Robot Security. WP6 Access control and Authorization for Internet of the Things.
Projects with HiTec and telecom providers:
- Security Architecture for a Supply Chain Management System based on Block-Chain
- CLOUD-PKI: Cloud Certification services based on HSM cryptography module.
- Android Software Security Evaluation
Sierra is also the director of the VICEROY DECREE virtual institute.
Recent publications
-
Developing an automated planning tool for non-player character behavior
Citation: Diego Romero, Mario Sánchez , José M. Sierra, Maximiliano Miranda, Federico Peinado. (2020). Developing an automated planning tool for non-player character behavior CoSECivi, 69-77. http://ceur-ws.org/Vol-2719/paper7.pdf -
Blockchain-based semi-autonomous ransomware
Citation: Oscar Delgado-Mohatar, José María Sierra Camara, Eloy Anguiano. (2020). Blockchain-based semi-autonomous ransomware Future Gener. Comput. Syst., 112, 589-603. https://doi.org/10.1016/j.future.2020.02.037 -
Lightweight Access Control System for Wearable Devices
Citation: Fidel Paniagua Diez, Diego Suarez Touceda, José María Sierra Camara, Sherali Zeadally. (2019). Lightweight Access Control System for Wearable Devices IT Prof., 21, 50-58. https://doi.org/10.1109/MITP.2018.2876985